CMMC

The Department of Defense developed the Cybersecurity Maturity Model Certification (CMMC) to protect the American Defense Industrial Base from cybersecurity threats. TrustNet’s security experts have the knowledge, experience, and technology to help clients achieve certification.
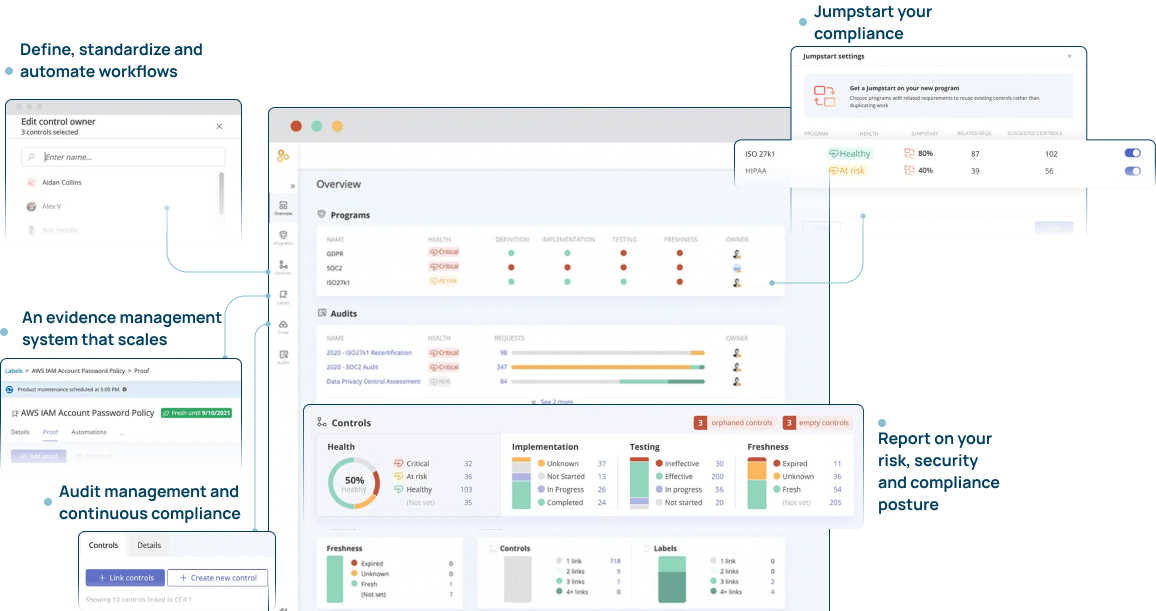
Compliance Management Platform
CMMC Audit Management and Continuous Compliance by Experts
WHAT IS CMMC ?
The CMMC was created by the DoD to enhance the security posture of the Defense Industrial Base (DIB) sector. The model is specifically designed to enforce protection of sensitive unclassified information that is shared by the Department with its contractors and subcontractors.The framework requires for the standardization of cybersecurity best practices and processes to secure both networks and data.
WHO CAN PROVIDE CMMC CERTIFICATION ?
Independent CMMC certification is performed by CMMC Third Party Assessment Organization (C3PAOs) or in some instances by the DoD. Certification providers must meet stringent DoD requirements to perform CMMC assessments.
HOW LONG IS AN ASSESSMENT VALID FOR ?
WHAT LEVEL OF CMMC MUST I ACHIEVE TO DO BUSINESS WITH THE DOD ?
Every DoD RFI (Request for Information) or RFP (Request for Proposal) will list the CMMC level required to meet the minimum standard for that contract.
Each CMMC level requires a designated number of practices and processes. Each level is a building block to the next level, requiring a greater number of controls and more stringency.
THE 3 LEVELS OF CMMC
LEVEL 1
Basic cybersecurity practices. Addresses the protection of FCI.
15 practices are required for the basic safeguarding requirements specified in 48 CFR 52.204.21.
LEVEL 2
110 practices aligned to NIST SP 800-171, including
- Analyzing and triaging events
- Audit log review
- Event detection and reporting
- Incident response
- Data backup and testing
- Encryption
LEVEL 3
110+ practices aligned to NIST SP 800-171 and SP 800-172 including:
- Defining procedures of CUI data handling
- Collecting audit info in central repositories
- Periodic risk assessments
- Cyber threat intel response plan
- Separate management of non-vendor-supported products
- Risk mitigation plan
- Email forgery protection
- Security assessment of enterprise software
- DNS filtering
- Sandboxing
- Restriction of CUI publication
- Spam protection mechanisms
TrustNavigator™ our proprietary service approach:
PLANNING
SCOPING
TESTING
REPORTING
Why Should I Choose TrustNet?
TrustNet has deep technical experience serving clients of all sizes, across multiple industries. We provide high quality professional services to help clients achieve CMMC certification quickly and efficiently.


