ISO/IEC 27001 CERTIFICATION
TrustNet provides ISO 27001 Certifications to organizations that are ready to undergo their ISO audit. ISO 27001 is the internationally recognized standard that outlines the requirements for constructing a risk-based framework to initiate, implement, maintain, and manage information security within an organization. The standard, based on the Plan-Do-Check-Act model, defines what an information security management system (ISMS) is, what is required to be included within the ISMS, and how management should form, monitor, and maintain the ISMS.
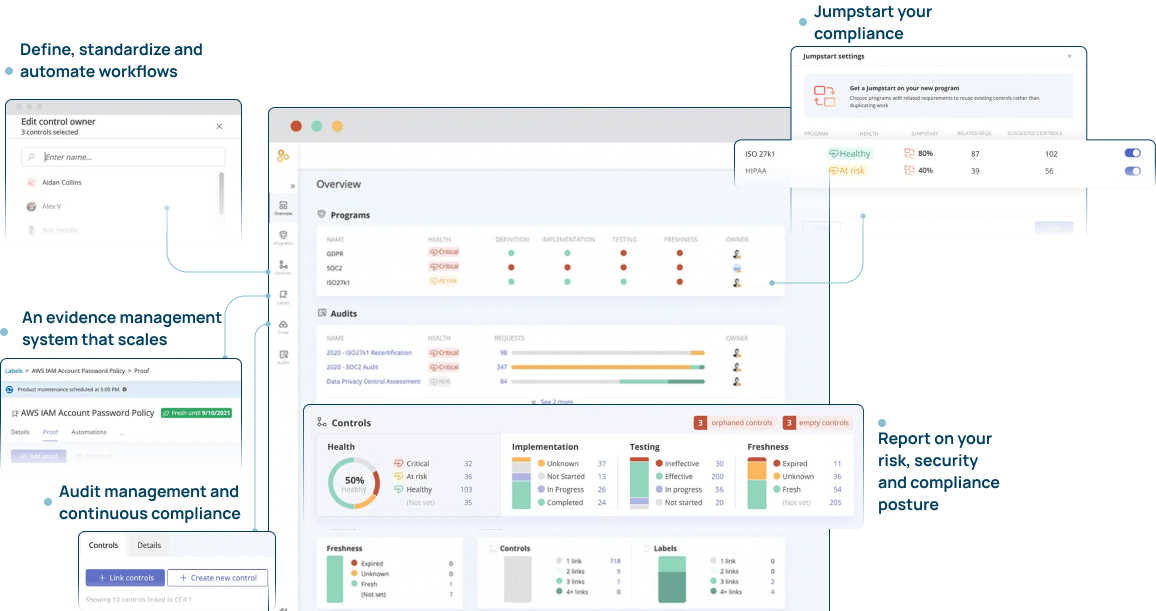
Compliance Management Platform
ISO/IEC 27001 Audit Management and Continuous Compliance by Experts
ISO 27001 Certification Service include:
ISO/IEC 27001 Gap Assessment
- Conduct an independent assessment to determine the readiness of the organization to undergo an ISO 27001 certification
- Examine the management system through documentation review and interview sessions to identify gaps
- Provide a gap assessment report including prioritized remediation action items
Project deliverables include the following:
- Information Security Management System (ISMS) Scope
- Risk Assessment
- Risk Treatment
- Gap Assessment
Certification Process
Regardless of size, today’s businesses need to work hard to protect the safety of their systems, applications, and data. In response, many choose to implement an Information Security Management System (ISMS) that is certified to comply with the ISO 27001 standard. Doing so demonstrates to management and stakeholders that fostering a secure environment is at the top of your corporate priorities list.
To get the certification, an organization must develop an ISMS containing security-related policies, procedures, technology, and qualified staff. Once this is completed, they must conduct an internal audit of the ISMS, addressing and taking action to correct any areas of concern.
Achieving certification requires enlisting the services of a qualified third-party body. This entity will thoroughly review the company’s ISMS to assess whether it meets ISO 27001 guidelines, a process that can take anywhere from three to 12 months from start to finish.
Initial Certification Review – Stage 1
Initial Certification Review – Stage 2
Surveillance Audits
TrustNavigator™ our proprietary service approach:
PLANNING
project planning and management
SCOPING
TESTING
REPORTING


